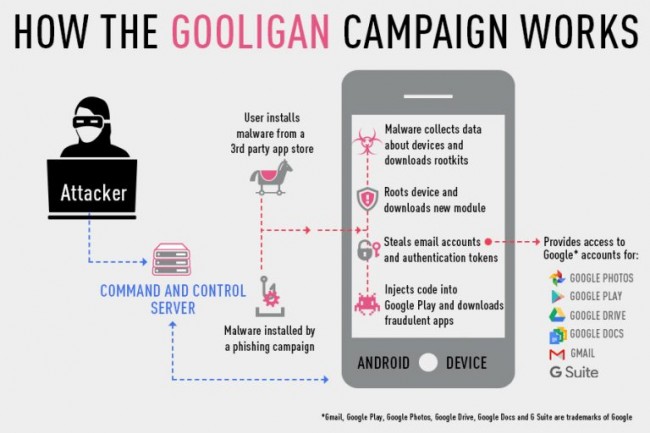
Over one million Google accounts have now been compromised following from a huge fraud campaign that targeted Android users and the Google Play store. The new malware infecting devices is known as Gooligan and it works by hiding inside of several Android apps and then exploiting two unpatched flaws to root devices and gain access to email account information.
From there, this malware can use its rooted access to silently install other selected apps from the Google Play store in order to boost in-app advertising revenue. This means that rather than harvesting user information for future scams, Gooligan is actually seeking a payout from advertising platforms, such as Google AdSense, which supplies advertising for YouTube and websites. Attackers also made some money from every app install.
Image Credit: Check Point
Check Point, a security research specialist was the first to point out the issue to Google after discovering that over one million Android devices have likely been affected since Gooligan first appeared back in August. Since then, around two million infected app installs have apparently taken place.
Details of this attack were released today but Google has already revoked all affected token access used to verify apps on Android devices. All Gooligan-infected apps have also been added to a block list. The malware may have infected over one million devices, but it could only work on select versions of Android, including Jelly Bean, KitKat and Lollipop, which make up a majority portion of the Android market.
Discuss on our Facebook page, HERE.
KitGuru Says: Google has always been a bit more relaxed when it comes to content control on the Play Store, which has led to a bloated marketplace of over two million apps. If something like this managed to slip through the cracks, I wonder how many other potentially dangerous apps are still floating around.
 KitGuru KitGuru.net – Tech News | Hardware News | Hardware Reviews | IOS | Mobile | Gaming | Graphics Cards
KitGuru KitGuru.net – Tech News | Hardware News | Hardware Reviews | IOS | Mobile | Gaming | Graphics Cards