Everything your phone transmits to and receives from your network providers phone tower is encrypted, so that only the network operator can receive your calls and data and route them as you request. This is all encrypted with a set of keys on the sim card inside your phone and another set held by the network provider, this should ensure that nobody can intercept and listen in to communications between your phone and the mobile phone tower. Unfortunately if anyone else has the network providers encryption keys, then this is no longer the case. The NSA and GCHQ have these keys.
In the latest Snowden leak (yes these revelations are still coming out) it seems that a joint task force made up of operatives from both the US NSA and the British GCHQ formed the Mobile Handset Exploitation Team (MHET) in April 2010. This team has done everything it can to totally undermine the security of the mobile infrastructure that we have in place today.
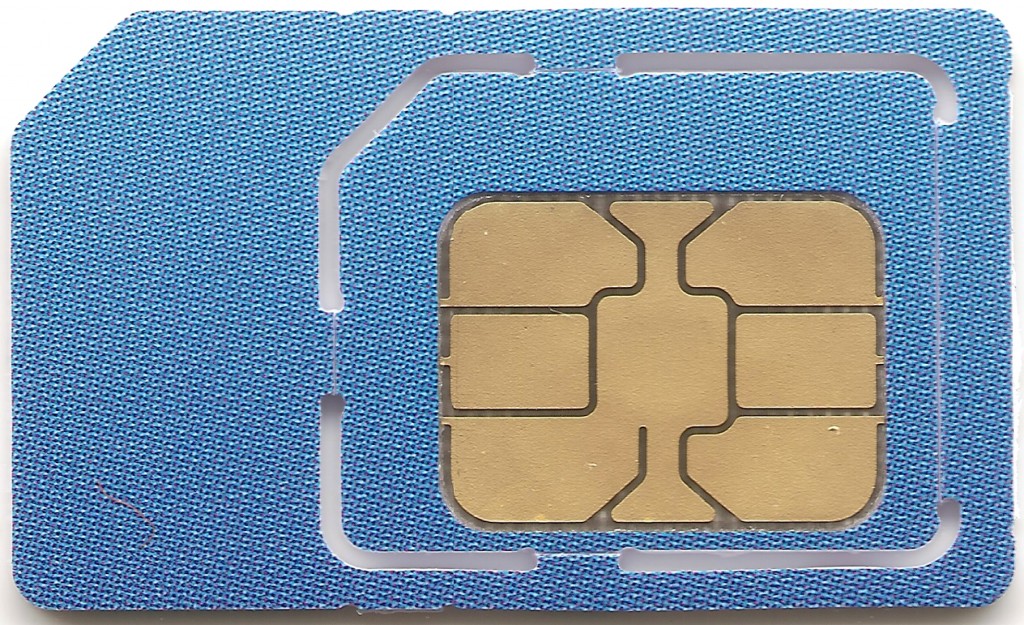
One of the main things listed in the top-secret documents provided to The Intercept by Edward Snowden is the fact that the MHET targeted a sim card company in the Netherlands that makes 2 billion SIM cards a year. They targeted Gemalto by spying on its employees, both sales staff and engineering teams and have boasted that “[We] believe we have their entire network”.
They also have the encryption keys, known as a “Ki”, for every sim produced and seem to have, or at least had access to the authentication servers that generate these keys. This means that they would be able to intercept and decrypt live calls on any network that was using Gemalto sim cards, some 450 wireless network providers around the world in 85 countries. This would be without any warrant needed and neither the user nor the network operator would be any the wiser. Christopher Soghoian, the principal technologist for the American Civil Liberties Union said, “The news of this key theft will send a shock wave through the security community.”
Discuss on our Facebook page, HERE.
KitGuru Says: The only silver lining here is that apps that pass encrypted data over these connections are still secure as far as we know. So the likes of TextSecure, SilentText, Signal and Whatsapp should still be out of the line of fire.
Source: The Intercept
 KitGuru KitGuru.net – Tech News | Hardware News | Hardware Reviews | IOS | Mobile | Gaming | Graphics Cards
KitGuru KitGuru.net – Tech News | Hardware News | Hardware Reviews | IOS | Mobile | Gaming | Graphics Cards


