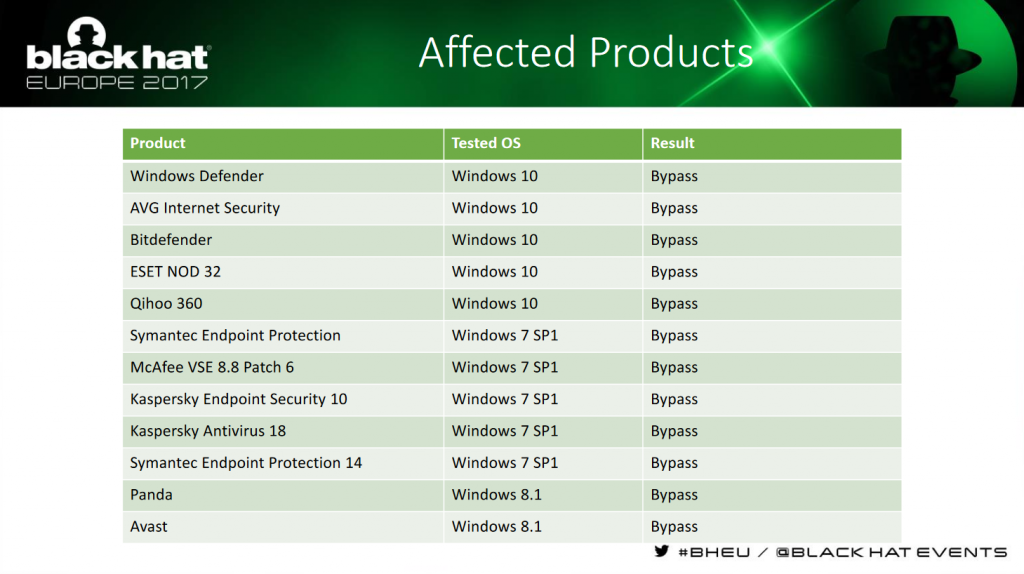
With every Windows update, your PC gets strengthened against attacks that are both old and new. All versions, however, are vulnerable to a new fileless code injection technique dubbed Process Doppelgänging, as no antivirus can handle it.
The process was discovered by Black Hat Europe, in which researchers Eugene Kogan and Tal Liberman detail it as similar to the now outdated Process Hollowing. This older technique is essentially a bait and switch, replacing memory of a legitimate program with modified, and potentially dangerous code that acts as if it is running as was intended.
That technique has already been caught and antivirus software has adapted to counter it. Process Doppelgänging, however, makes use of how all modern versions of Windows run programs that were originally designed for Windows XP.
Step by step, the exploit sends an ordinary executable to be handled by the NTFS transaction, only to be overwritten by a malicious file. The NTFS transaction purposefully avoids partial operations with its sandboxed location returning either a success or failure. Once a piece of memory in the original file is modified, the NTFS transaction is intentionally failed so that the original file appears unmodified. In turn, the Windows process loader can call upon the modified section that was never removed to execute its harmful components.
This method still works on the latest Windows 10 version, beyond the Fall Creators Update, despite briefly being stopped by a blue screen of death a couple of updates prior. Microsoft and antivirus vendors have yet to officially comment on the matter, but the latter will certainly be working on some fixes in the coming weeks.
KitGuru Says: It’s a good thing that security researchers find these things before too many victims fall prey to it. I’d take a blue screen of death over being victim to Process Doppelgänging, even if it isn’t a desired solution.
 KitGuru KitGuru.net – Tech News | Hardware News | Hardware Reviews | IOS | Mobile | Gaming | Graphics Cards
KitGuru KitGuru.net – Tech News | Hardware News | Hardware Reviews | IOS | Mobile | Gaming | Graphics Cards