Edward Snowden is back in the news again today, after detailing to Wired during an extensive interview, that the NSA is working on a system that will not only be able to pinpoint DDOS and other more nefarious attacks against the US and shut them down automatically, but potentially even launch its own counter attacks against those responsible. The worrying part, is that this is all being designed to operate autonomously, therefore responding more quickly, but potentially without the go ahead of anyone with a pulse.
It should be said at this point, that the system, which Snowden says is codenamed MonsterMind, has far less evidence supporting its existence than other NSA schemes like PRISM, which are well documented. However Snowden insists that it exists and that it was still undergoing development when he left the NSA last year in order to blow the whistle on many of the intelligence agency's intrusive snooping techniques.
The idea behind the system according to Snowden, is for MonsterMind to look at the metadata surrounding all web traffic, pinpointing spikes in certain behaviours and identifying them as malicious activity. If that activity is aimed at US infrastructure, such as an attempt to shut down banks, public communication networks or transport systems, it could initiate measures to block the attack through a variety of measures. If needed, it could potentially then launch a counter attack to cripple the system responsible and perhaps even identify those behind it.
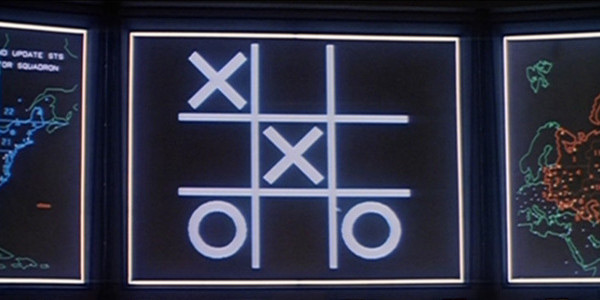
For the love of god, somebody break out naughts and crosses before it's too late!
As with PRISM, this would understandably be an invaluable tool for anyone looking to defend a country, but it has worrying implications for US citizens and web users across the world. For starters, any sort of attack from foreign soil, is going to be hidden, which means routing it through some sort of public bot net, or potentially even the systems of another country. In either case, if MonsterMind weighs in and attacks those systems, it could create an international incident without anyone giving it the go ahead. Similarly, end users could find their machines inoperable, or could potentially even find themselves accused of digital terrorism.
As cryptographer Matt Blaze points out to Wired though, it seems unlikely that the NSA wouldn't take into consideration that this sort of situation would arise, so it has likely built safeguards in place – though the fact that a contractor managed to steal thousands of classified documents does make you wonder how well thought out anything at the NSA really is.
What is perhaps a bigger issue, is how MonsterMind would identify traffic as malicious in the first place. Blaze suggests that in order to make that a reality, it would need to monitor all web traffic, at least all of it going in and out of the United States. The NSA already collects metadata on calls, emails and other communications and some content, but a scheme like this would see that surveillance extended way beyond its current limitations, easily breaching the fourth amendment right of seizing private communications without a warrant.
 KitGuru KitGuru.net – Tech News | Hardware News | Hardware Reviews | IOS | Mobile | Gaming | Graphics Cards
KitGuru KitGuru.net – Tech News | Hardware News | Hardware Reviews | IOS | Mobile | Gaming | Graphics Cards



oh shit